A state-sponsored threat actor allegedly affiliated with Iran has been linked to a series of targeted attacks aimed at internet service providers (ISPs) and telecommunication operators in Israel, Morocco, Tunisia, and Saudi Arabia, as well as a ministry of foreign affairs (MFA) in Africa, new findings reveal.
The intrusions, staged by a group tracked as Lyceum, are believed to have occurred between July and October 2021, researchers from Accenture Cyber Threat Intelligence (ACTI) group and Prevailion’s Adversarial Counterintelligence Team (PACT) said in a technical report. The names of the victims were not disclosed.
The latest revelations throw light on the web-based infrastructure used by Lyceum, over 20 of them, enabling the identification of „additional victims and provide further visibility into Lyceum’s targeting methodology,” the researchers noted, adding „at least two of the identified compromises are assessed to be ongoing despite prior public disclosure of indicators of compromise.”
Believed to be active since 2017, Lyceum (aka Hexane or Spirlin) is known to target sectors of strategic national importance for purposes of cyber espionage, while also retooling its arsenal with new implants, and expanding its sights to include ISPs and government agencies. The new and updated malware and TTPs have enabled the hacking group to mount attacks against two entities in Tunisia, Russian cybersecurity firm Kaspersky disclosed last month.
The threat actor has been traditionally observed using credential stuffing and brute-force attacks as initial attack vectors to obtain account credentials and gain foothold into targeted organizations, leveraging the access as a springboard to drop and execute post-exploitation tools.
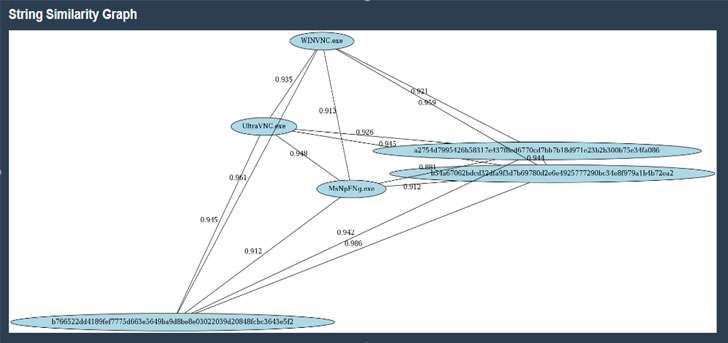
Two distinct malware families — called Shark and Milan (named „James” by Kaspersky) — are the primary implants deployed by the threat actor, each allowing for the execution of arbitrary commands and exfiltration of sensitive data from the compromised systems to a remote attacker-controlled server.
ACTI and PACT also said it located beaconing from a reconfigured or potentially a new Lyceum backdoor in late October 2021 originating from a telecommunications company in Tunisia and an MFA in Africa, indicating that the operators are actively updating their backdoors in light of recent public disclosures and attempting to bypass detection by security software.
„Lyceum will likely continue to use the Shark and Milan backdoors, albeit with some modifications, as the group has likely been able to maintain footholds in victims’ networks despite public disclosure of [indicators of compromise] associated with its operations,” the researchers said.




