A group of academics from the North Carolina State University and Dokuz Eylul University have demonstrated what they say is the „first side-channel attack” on homomorphic encryption that could be exploited to leak data as the encryption process is underway.
„Basically, by monitoring power consumption in a device that is encoding data for homomorphic encryption, we are able to read the data as it is being encrypted,” Aydin Aysu, one of the authors of the study, said. „This demonstrates that even next generation encryption technologies need protection against side-channel attacks.”
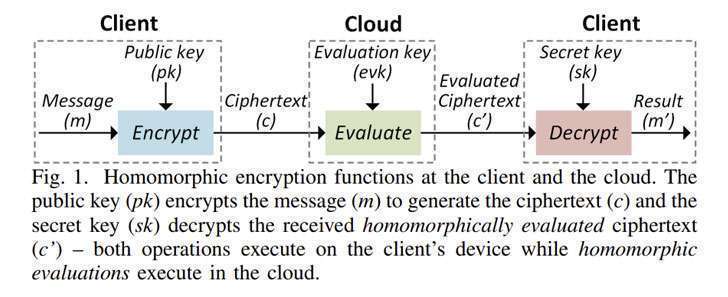
Homomorphic Encryption is a form of encryption that allows certain types of computation to be performed directly on encrypted data without having to decrypt it in the first place.
It’s also meant to be privacy-preserving in that it allows sharing of sensitive data with other third-party services, such as data analytics firms, for further processing while the underlying information remains encrypted, and by extension, inaccessible to the service provider.
Put differently, the goal of homomorphic encryption is to facilitate the development of end-to-end encrypted data storage and computation services where the data owner never needs to share their secret keys with third-party services.
The data leakage attack proposed by the researchers involves a vulnerability discovered in Microsoft SEAL, the tech giant’s open-source implementation of the technology, which could be exploited in a manner that allows the recovery of a piece of plaintext message that’s being homomorphically encrypted, effectively undoing the privacy protections.
Specifically, the attack, dubbed RevEAL, „targets the Gaussian sampling in the SEAL’s encryption phase and can extract the entire message with a single power measurement,” by taking advantage of a „power-based side-channel leakage of Microsoft SEAL prior to v3.6 that implements the Brakerski/Fan-Vercauteren (BFV) protocol,” the researchers said.
The researchers noted that SEAL versions 3.6, released on December 3, 2020, and later use a different sampling algorithm, while cautioning that newer versions of the library may suffer from a „different vulnerability.”
„Encryption error is sampled from a Centered Binomial Distribution (CBD) by default unless 'SEAL_USE_GAUSSIAN_NOISE’ is set to ON,” Kim Laine, Microsoft’s principal research manager who heads the Cryptography and Privacy Research Group, said in the release notes.
„Sampling from a CBD is constant-time and faster than sampling from a Gaussian distribution, which is why it is used by many of the NIST PQC finalists,” Laine further added.




